Initially, blockchain was used for creation of cryptocurrencies, but today the scope has expanded. Blockchain is used in the financial industry, smart contracts, healthcare, the gaming industry, fine arts, music, real estate, insurance, logistics, government, etc., because it allows you to store almost any information. Along with the spread of technology, the security risks of blockchain have also increased. Attackers are actively looking for blockchain vulnerabilities in order to gain access to user data. Examples of such activities are delaying the chain, cancelling transactions made on the blockchain, stealing users’ private keys, and more.
To understand how blockchain technology can best help protect identities, you need to understand how it works.
What is Blockchain?

A blockchain, or literally “block chain,” is a digital database containing information that can be shared across a large, decentralized, public network.
Blockchain consists of blocks of information that follow each other in a strictly defined order. Each block contains records about the previous block, as well as the data that is written to it. Examples of such data could be:
- transaction information;
- information about how much cryptocurrency belongs to a particular user;
- information about the owner of the assets and much more.
Thus, blockchain is a technology for storing information. Its main feature is that there can be many copies of the blockchain, and they are stored simultaneously on different computers (called nodes).
The information stored on the blockchain cannot be changed. Attackers can hack 1 node and make changes to the blockchain. Other nodes will not accept these changes unless they are approved by 51% of the nodes. It is impossible to hack hundreds of thousands of nodes at once. However, attackers exploit other security issues in blockchain technology.
The principle of blockchain technology
The easiest way to understand the operation principle of blockchain is the example of cryptocurrency transactions. They are often the target of hackers who want to seize other people’s funds.
Blockchain is located on computers all over the world. Anyone with an internet connection can access it. The computers of miners (for PoW blockchains) and validators (for PoS blockchains) are used for creation and storage of blocks. These computers are responsible for detecting transaction requests from users, aggregating them, validating them, and adding them to the blockchain as new blocks.
Ownership in the blockchain is determined by 2 types of keys: open/public and secret/private. The public key is stored in the blockchain in clear text. The second, private, key is kept by the owner. These keys are used for encryption and signing. Transactions are signed with private keys corresponding to public keys.
To ensure transactions are irreversible, all miners and validators on the network must have the same copy of the blockchain. When a new block is added, the miner or validators provide a cryptographic proof of the transaction. To get a proof, the miner or validator passes the block through several rounds of the hash function.
7 types of blockchain attacks
As stated above, the blockchain uses a distributed immutable ledger. It is quite difficult to hack it, but there are still blockchain vulnerabilities that can compromise the entire operation of the technology. Using them, attackers can build such 7 common attacks.
51% attacks
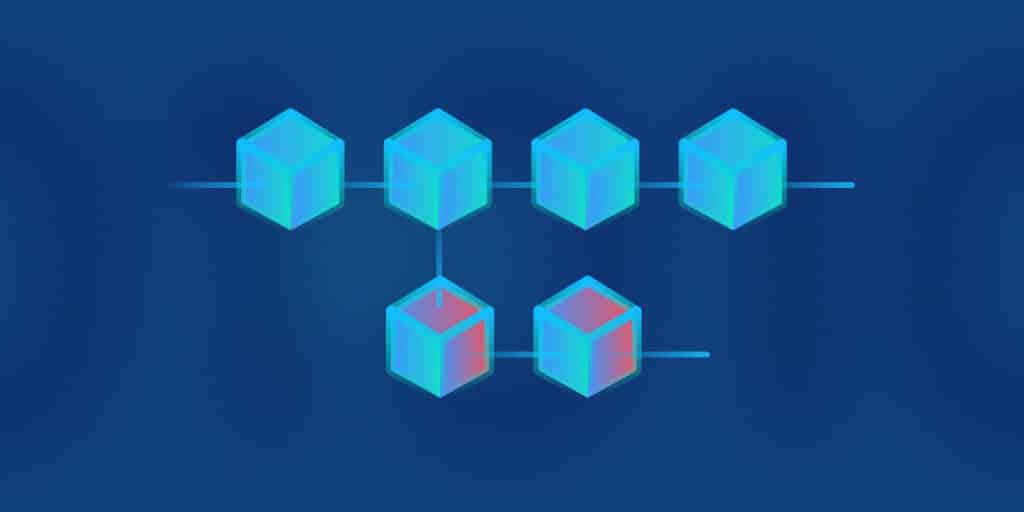
In blockchain technology, the approval of blocks requires the support of 51% of the network (consensus). Sometimes a situation arises when 2 blocks with conflicting transactions are processed. Only the block that received consensus approval will remain on the chain. The second one will be regarded as outdated.
Imagine that the necessary 51% of the network fell under the control of intruders. They can use their majority to cancel transactions or conduct fraudulent operations. Even changing some blocks becomes possible, although hackers are unlikely to be able to rewrite the entire chain.
Young blockchains are particularly susceptible to 51% attacks. When there are still few participants in the network, it is much easier to gain control over more than half of the network than in a developed network with thousands of participants.
In 2019, the giant of the cryptocurrency market Ethereum Classic was subjected to the 51% attack. For 3 days, the price of the cryptocurrency fell by 16.4%, and the attack brought more than USD 1 million to the scammers.
Sybil attacks
The name was chosen after the main character of Flora Rheta Schreiber’s bestselling book Sybil, about the treatment of dissociative identity disorder. This is a way to attack a peer-to-peer network. Scammers create fake nodes to which the victim connects. Thanks to this, a hacker can obtain the necessary majority consensus (51%) and disrupt transactions on the blockchain. At its core, a Sybil attack is a 51% attack.
A simple example of a Sybil attack is the creation of multiple online accounts that belong to the same person. To other participants, they will look independent, but they are all controlled by a scammer (or a group). The nodes controlled by a scammer are able to persuade other network nodes to approve corrupted data.
Double-spend attacks
Double-spend occurs when a scammer spends the same coins twice: user 1 sends the same 10 coins to user 2 and user 3 at the same time. If the blockchain works properly, only one transaction will receive majority approval. In most cases, this is what happens. The blockchain has built in mechanisms to prevent such attacks. For example, if a coin is sent to user 2 in the first block, the transaction to user 3 will be ignored in subsequent blocks.
Types of double-spend attacks:
- The Race attack involves the simultaneous sending of 2 opposite transactions with the same funds, but only one of them is confirmed. The goal is to send the stolen coins to the right address and cancel the other payment. The attack is possible only if this blockchain supports zero-confirmation transactions.
- The Finney attack is also possible only if zero-confirmation transactions are supported. One of the transactions is written to a block, which is stored by the malicious miner. Subsequently, the same coins are spent in another transaction. The previously recorded block is broadcast to the network, and the second transaction is invalidated. However, the sale of the goods has already taken place, which means that the scammers have received their benefit.
- Brute force attack requires powerful equipment. It works even in cases where more than 1 confirmation is used to confirm transactions. The fraudster independently checks the blocks in which transactions are recorded, including his own. As a result, the seller receives the required number of confirmations and transfers the goods. After that, the fraudster can fork the network and invalidate the transaction.
In the case of cash, you pay with a banknote and give it to another person. You cannot pay with the same banknote twice. With digital currencies, everything is different. Cryptocurrency is an entry in the blockchain, so theoretically it can be reproduced.
Routing attacks
Routing attacks are not directly related to security issues in blockchain technology. They exploit vulnerabilities in ISP connection protocols. Blockchain uses the network to operate, so it depends on providers. They connect to each other using the Border Gateway Protocol (BGP).
Attackers who gain access to this protocol can publish false routes. This will lead to the prohibition of some transactions and even the division of the blockchain network into two. Usually, these are uneven parts with a different number of participants.
Hackers act as a link between the 2 halves of the network, and all data passes through them. After the attack stops, the blocks in the smaller half of the network will be reset. This will lead to a flood of transactions and the ability to receive any rewards for mining.
Routing attacks are also used to delay the delivery of new blocks. While the attack lasts, the block remains invisible on the network, and this allows a double-spend attack.
Routing attacks can have serious consequences. Using secure routing protocols will help prevent this type of attack on the blockchain.
Private key attacks
How asymmetrical encryption technology, which is also used in blockchain, can help protect confidential data Open (public) and closed (private) key cryptography is used for this. This technology provides confidential communication in open channels. Knowing the user’s public key, the other party can encrypt the message for them. The user will be able to read it by decrypting it with their private key. Other private keys will not allow the message to be opened.
The public and private keys are interconnected. If you have a private key, then you can recover the public key. However, this scheme does not work in the opposite direction.
Attackers sometimes gain access to a private key due to its owner’s negligence. An example of such a situation would be the case when a private key is stored on a computer that has been hacked. Phishing is also used to obtain private keys. As a result, the key gets to the scammers, and with its help they can easily take possession of the user’s entire cryptocurrency assets.
Selfish mining attacks
Selfish mining aims to get more rewards. The easiest way to understand the principle of such mining is with an example.
The hashrate is evenly distributed by 25% between 4 miners: the first, the second, the third and the fourth. The first three play by the rules: once a block is found, they add it to the chain. But the fourth miner wants to get more profit. When he/she finds a block (or two), he/she holds it.
The first three miners have found 10,000 blocks and want to offer the 10,001st. The fourth miner has already found the 10,002nd, but keeps it a secret. With some luck, he/she can always be ahead of the public chain by 1-2 blocks. Thus, the public chain of the fourth miner will be longer, and the longer chain is always recognized as correct. The longer the fourth miner will play such a game, the greater the reward he/she will receive. When his/her chain becomes the main one, he/she will receive a reward for all blocks starting from the 10,001st.
By pooling, selfish miners can get serious power and attempt 51% attacks.
Vulnerable Smart Contacts
Smart contracts are used in the blockchain to make transactions. For example, by lending cryptocurrencies at interest, you can enter into a smart contract and make a corresponding entry in the blockchain. Such records are stored in encrypted form, however, flaws in the code can lead to hackers gaining access to the contract.
The main vulnerabilities of smart contracts:
- reentrancy;
- access control;
- arithmetic features;
- lack of checking the return values of low-level calls;
- denial of service;
- the problem of pseudo-random numbers;
- race;
- time dependency;
- address length manipulation.
The most famous and largest thefts: USD 30 million from Parity and USD 53 million from DAO.
Preventing Blockchain Security Issues

The following actions will help increase the security of the blockchain:
- Using Proof of Stake instead of Proof of Work will be a solid defence against 51% attacks. The decision will go to the users who own the majority of the coins.
- There are several algorithms to prevent Sybil attacks. Proof of Work is used in most cryptocurrencies.
- Miner pool control will help fight selfish mining. As soon as the pool gets more than 40% of the power, it must transfer some of the miners to another pool. This contributes to the decentralization of the network.
- Secure protocols help protect against routing attacks.
- Smart contracts must be audited before implementation.
Also, do not forget about the secure storage of private keys, the use of reliable email and two-factor authentication.
Conclusion
Making a blockchain secure requires a thorough audit. As the financial value grows, the risks of the blockchain also increase. The cost of an audit may seem high, but it’s a small cost compared to the losses that can result from hacker attacks. Regular in-depth audits from H-X Technologies will help keep blockchain security at a high level.
