Server hardening
FAQ
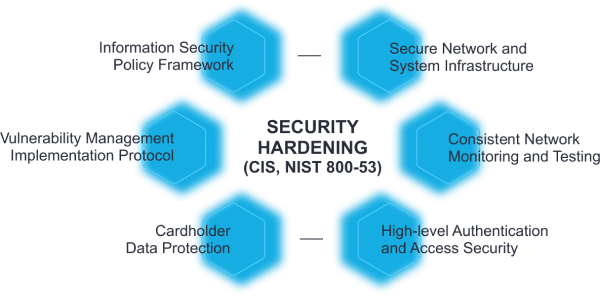
Server hardening refers to the process of improving the security of a server by reducing its attack surface and minimizing potential vulnerabilities. It involves configuring the server software and operating system to remove or disable unnecessary services and functions that could be exploited by attackers.
The goal of server hardening is to make it more difficult for unauthorized users to gain access to sensitive data or compromise the server's functionality.
The primary objective of server hardening is to enhance the security of a server by reducing its attack surface and minimizing the risk of unauthorized access, data theft, and other types of cyber threats.
By implementing server hardening measures, organizations can reduce the likelihood of successful attacks, prevent data loss or corruption, and maintain the confidentiality and integrity of sensitive information. Additionally, server hardening can help organizations comply with regulatory requirements and industry standards related to data security and privacy.
Some specific objectives of server hardening include:
- Reducing the risk of exploitation of known vulnerabilities
- Removing or disabling unnecessary software, services, and functions
- Implementing access controls and limiting user privileges
- Configuring firewalls and intrusion detection/prevention systems
- Enforcing strong passwords and authentication mechanisms
- Implementing encryption to protect data in transit and at rest
- Monitoring server activity and reviewing logs for potential security incidents
There are several types of system hardening that organizations can implement to improve the security of their systems. Some of the most common types include:
- Operating system hardening: This involves configuring the operating system to remove or disable unnecessary services, ports, and features that could be exploited by attackers. This includes installing security patches and updates, configuring access controls, implementing encryption, and enforcing strong password policies.
- Network hardening: This involves securing the network infrastructure by implementing firewalls, intrusion detection/prevention systems, and other security measures to prevent unauthorized access and data exfiltration.
- Application hardening: This involves securing the applications that run on the system by implementing secure coding practices, input validation, and error handling, and using security testing tools to identify and remediate vulnerabilities.
- Database hardening: This involves securing the database infrastructure by implementing access controls, encrypting sensitive data, and using auditing and monitoring tools to detect and respond to potential security incidents.
- Physical hardening: This involves securing the physical environment in which the system is located by implementing access controls, using surveillance cameras, and implementing environmental controls to prevent damage from fire, water, or other hazards.